PESHAWAR: A database allegedly linked to a Khyber Pakhtunkhwa government website has been shared on the dark web, raising concerns about potential exposure of sensitive internal data. The leak, attributed to a threat actor which is unnamed, is said to involve the domain Government of Khyber Pakhtunkhwa.
According to details circulating online, the dataset is being offered through publicly accessible download links in compressed file formats. The tweet goes on to claim that the database is from “http://iams.kp.gov.pk”, associated with Khyber Pakhtunkhwa (KP), Pakistan. Keen-eyed enthusiasts will also notice that the URL is HTTP instead of the standard HTTPS that ensure encryption and prevention of data access from third-parties.
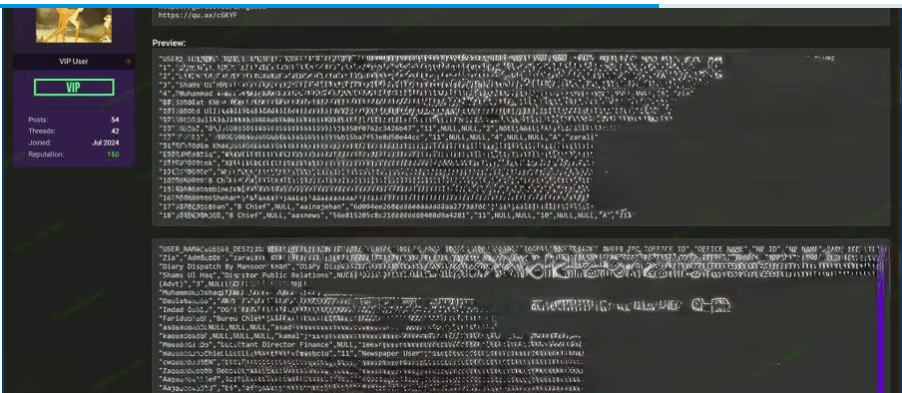
Preview samples accompanying the leak suggest the presence of user-related information, including login names, passwords, and access roles.
The preview data reportedly contains fields including login names, passwords, user access levels, department identifiers, and office-level organizational data. The presence of fields such as LOGIN_NAME, LOGIN_PASS, and USER_LEVEL suggests the database may be linked to an internal system or administrative panel, rather than a public-facing service. Whether the passwords are stored in plaintext or as hashed values remains unclear from the available samples.
Passwords used such as “pak@123, dg@12345, kamal@12345, asad@12345” for a sensitive database such as that of a provincial government makes many wonder if cybersecurity is nothing but a joke in Pakistan.
Threat intelligence analysts flagged several possible explanations for how the data became accessible. These include a misconfigured server that left the database exposed without authentication, a credential compromise that gave the attacker direct access, or a previously unreported breach that is only now surfacing publicly.
Pakistan’s government domains have been targeted in a number of previous incidents, and security researchers have repeatedly noted that public sector digital infrastructure in the country faces persistent vulnerability due to legacy systems and inconsistent security practices.
The risks associated with this type of leak are significant even if the data is partially outdated. Government credential leaks carry elevated risk regardless of age, since users frequently reuse passwords across systems and may not change credentials even after a previous exposure. Organizations affected by such leaks are advised to force password resets, audit access logs for unusual activity, and review server configurations for unintended public exposure.
The incident was flagged by the threat intelligence source “Dark Web Intelligence,” shared via the account @DailyDarkWeb on X. The authenticity and recency of the database have not been independently verified. The KP government has not publicly acknowledged the alleged breach or issued any statement at the time of writing.